Get all set for a facepalm: 90% of credit history card audience now use the same password.
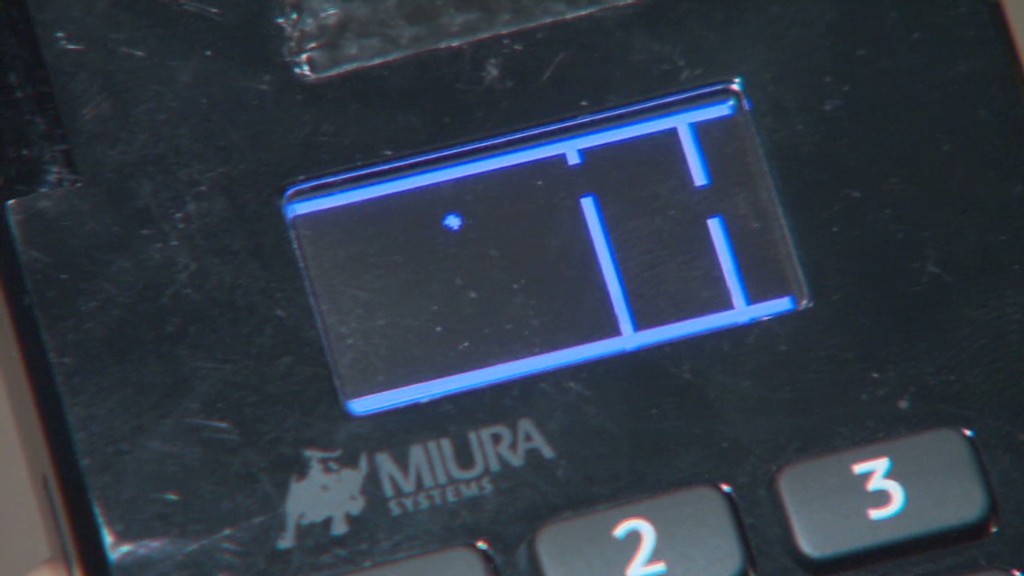
The passcode, set by default on credit card equipment considering that 1990, is quickly identified with a speedy Google searach and has been exposed for so lengthy there is certainly no perception in making an attempt to hide it. It truly is possibly 166816 or Z66816, based on the machine.
With that, an attacker can achieve entire regulate of a store’s credit rating card readers, probably allowing them to hack into the equipment and steal customers’ payment facts (believe the Goal (TGT) and Household Depot (High definition) hacks all in excess of once more). No speculate major merchants hold dropping your credit history card facts to hackers. Stability is a joke.
This newest discovery arrives from researchers at Trustwave, a cybersecurity organization.
Administrative accessibility can be applied to infect equipment with malware that steals credit score card details, defined Trustwave executive Charles Henderson. He detailed his results at previous week’s RSA cybersecurity conference in San Francisco at a presentation identified as “That Stage of Sale is a PoS.”
Get this CNN quiz — come across out what hackers know about you
The trouble stems from a match of incredibly hot potato. Machine makers market devices to specific distributors. These sellers provide them to stores. But no one particular thinks it can be their work to update the master code, Henderson instructed CNNMoney.
“No just one is transforming the password when they set this up for the initially time everybody thinks the safety of their position-of-sale is anyone else’s obligation,” Henderson explained. “We’re generating it pretty easy for criminals.”
Trustwave examined the credit card terminals at extra than 120 stores nationwide. That features major clothing and electronics outlets, as well as community retail chains. No particular retailers had been named.
The large majority of machines had been designed by Verifone (Pay back). But the same challenge is existing for all key terminal makers, Trustwave said.

A spokesman for Verifone claimed that a password alone is not adequate to infect equipment with malware. The corporation mentioned, until eventually now, it “has not witnessed any assaults on the safety of its terminals dependent on default passwords.”
Just in situation, while, Verifone reported vendors are “strongly suggested to adjust the default password.” And at present, new Verifone equipment come with a password that expires.
In any situation, the fault lies with vendors and their unique suppliers. It really is like home Wi-Fi. If you get a residence Wi-Fi router, it’s up to you to adjust the default passcode. Shops should really be securing their personal machines. And machine resellers should be serving to them do it.
Trustwave, which assists protect merchants from hackers, reported that retaining credit card equipment safe and sound is low on a store’s list of priorities.
“Providers spend extra cash deciding on the colour of the issue-of-sale than securing it,” Henderson stated.
This challenge reinforces the summary made in a current Verizon cybersecurity report: that stores get hacked because they are lazy.
The default password thing is a really serious difficulty. Retail laptop networks get uncovered to laptop or computer viruses all the time. Consider a person situation Henderson investigated recently. A awful keystroke-logging spy computer software ended up on the pc a shop employs to process credit rating card transactions. It turns out staff had rigged it to perform a pirated variation of Guitar Hero, and unintentionally downloaded the malware.
“It displays you the stage of accessibility that a great deal of folks have to the point-of-sale surroundings,” he said. “Frankly, it truly is not as locked down as it really should be.”
CNNMoney (San Francisco) 1st revealed April 29, 2015: 9:07 AM ET






More Stories
How Travel Directories Are Helpful for Common Travllers
Ten Little Known Facts About the Vacation Hot Spot of Wildwood, New Jersey
Discover Serenity at Svaha Spa Bisma